A friend just got her computer back from “the computer doctor.” Evidently it had been compromised with a root kit (the really nasty sort of software that runs at such a low-level your anti-virus software can’t see it). She uses three different anti-malware tools and was quite surprised that none of them caught it.
The problem with anti-virus software is it can only protect you against problems that are already known. The bad guys are constantly looking for new ways to attack your computer and the anti-virus programs are playing catch up. I’m not saying don’t use anti-virus software (the free version of Avast has saved me several times), just don’t count on it as your only defense.
So, is there any 100% guaranteed way to stop malware? Well, you could always unplug your computer from the Internet and never use it to access any USB drives or CDs, but that’s not exactly practical. And if you do stay online, even visiting only “known safe” sites doesn’t help much, since even legit sites get compromised on occasion.
But there are a few things you can do to help your odds. None of these approaches is 100% guaranteed to keep you safe, but they should help.
The Basics
This is “the usual stuff” you hear any time someone talks about how to stay safe online. It seems obvious, and yet it bears repeating because it’s easy to get careless:
- Don’t open attachments you weren’t expecting, not even from people you know and trust. Maybe that attachment from your friend Bob really is the really important document the email says, but if you weren’t expecting it, you have no way of knowing.
- Be skeptical of clicking links in unexpected emails. Your bank isn’t going to tell you to click a link to verify your account information. (If something like this ever does turn out to be legit, you need to change banks.)
- Don’t download pirated software. Aside from the legal issues, pirated software frequently contains malware.
Slightly more Difficult
Beyond the basics, there are a few other things that are easy enough to do, but don’t always make it into the “How to stay safe” discussions. Most attacks against your computer are targeting the applications you run, not the operating system. (Running Windows isn’t as risky as reading a PDF file with Acrobat reader.)
- Use a browser other than Internet Explorer. Microsoft’s made a lot of progress with the safety of Internet Explorer over the past few years. But even though IE recently dropped below 50% of the total browser market, it’s still the single most popular browser out there and therefore the one most likely to be targeted in online attacks.
- Keep your system up to date. Not just the Windows/Mac/Whatever Operating System patches, but also the software you use. Use Microsoft Update instead of Windows Update to get patches for Office. Install Secunia’s Personal Software Inspector tool to find out what other software on your computer is out of date.
- Uninstall software you don’t use. The more programs you have, the more likely you are to have something which has security problems. Bonus: You also save disk space!
- Run “alternate” software. The more widely-used a given program is, the more tempting a target it becomes for the bad guys. Instead of Acrobat Reader, use Foxit Reader. Instead of Microsoft Office, use Libre Office (fully compatible documents, but also available for free.)
- Uninstall Java. Most home users don’t need it, and older versions were not only laden with security problems, but the updates didn’t remove the older versions.
- Don’t run as the Administrator. When you set up your computer, reserve the main account for software installations and the like. Create a second, less-privileged login ID for day to day tasks.
Security journalist Brian Krebs talks a bit more about keeping software up to date and what to install or delete in his: 3 Basic Rules for Online Safety
Going for the Gusto
Wanna go really hard-core?
- Uninstall Flash (or install a flash blocker so that you have to approve any Flash scripts that run).
- Install NoScript (same idea).
- Don’t do any online banking with a Windows machine, use a Linux live CD instead. (For a business, I’d consider this one an absolute must.)
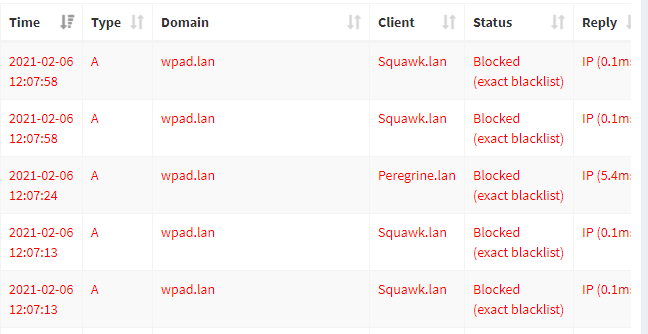
- Use a third-party DNS provider. Both Open DNS and Google Public DNS provide a facility where you change a couple system settings and if you then attempt to access a site which serves up malware, they’ll block the connection.
The Takeaway
There are no magic bullets. None of these suggestions will provide absolute protection for all users. What might be overkill for one person’s situation might not be nearly enough protection for another. But by choosing the practices which make the most sense for you personally, you can tilt the odds a bit more in your favor.
Bonus Reading: Get a Mac/Switch to Linux
In most discussions of online security, someone inevitably replies “Get a Mac!” or “Switch to Linux.” It’s a bit like going to a concert and someone yelling, “Play Freebird.” It’s a wonderful song, and a few groups have done great covers in response, but it’s not always the best fit.
But if the suggestion is inevitable, I may as well be the one to make it and bring up some of the tradeoffs.
Switching to a Mac may actually make sense for some folks, but don’t make the switch thinking you’ll be invincible. At the annual CanSecWest security conference, there’s a “Pwn2Own” contest where security professionals attempt to break into computers running the latest versions of the Mac OS, Windows and Linux. The first one to succeed, wins the computer. Every year, the Mac is the first system compromised.
Now that’s what happens at a security conference. Macs are less common than Windows computers; so the bad guys have to work harder to find them. It’s much easier to attack the more common computers.
But malware targeting Macs has been cropping up too.
Other concerns with switching to a Mac:
- You’ll have to buy all your software again. Assuming a Mac version even exists. Otherwise, you might have to look for an equivalent program.
- Despite the marketing pitch, a Mac doesn’t always “just work.” Just two weeks ago a co-worker returned a Mac Notebook that was downloading over his WiFi at just 1/10 the speed of Windows computer. (Apple’s support wasn’t able to resolve the problem.)
- You may encounter problems with incompatible file formats when sharing files with people who use Windows. Particularly if the programs you were using on Windows aren’t available for Mac and you had to switch to something else.
Linux tends to be the most secure OS of all (as noted earlier, most of the problems these days are the software you run on top of it). The main downfalls of Linux are:
- Availability. Yes, it’s free to get a copy, but you still have to find where to download it, burn a CD, and install it. Although this is getting easier, it’s still not a set of tasks the average home user will be comfortable with.
- Commercial software. Few software vendors on Windows or Mac have Linux versions of their software. Some do, but most do not. You’ll generally have to find an open source equivalent, and then work out how to share files with others who are on Windows or Mac.